Trustico® Online Security Blog
Say informed with the latest SSL Certificate news, security updates, and industry insights. Our articles cover everything from SSL Certificate management best practices to emerging cybersecurity trends and industry news.

SEO and SSL Certificates (SSL)
Trustico® SSL Certificates provide the HTTPS encryption that search engines look for when determining rankings. Sites secured with our SSL Certificates typically see improved search visibility and higher placement in results.
SEO and SSL Certificates (SSL)
Trustico® SSL Certificates provide the HTTPS encryption that search engines look for when determining rankings. Sites secured with our SSL Certificates typically see improved search visibility and higher placement in results.

SSL Certificate Sniffing Attacks
SSL Certificate sniffing occurs when attackers intercept encrypted traffic between a client and server by exploiting vulnerabilities in the SSL Certificate/TLS protocols. Without proper SSL Certificate security measures, sensitive data...
SSL Certificate Sniffing Attacks
SSL Certificate sniffing occurs when attackers intercept encrypted traffic between a client and server by exploiting vulnerabilities in the SSL Certificate/TLS protocols. Without proper SSL Certificate security measures, sensitive data...

Understanding SSL Certificate Bridging
SSL Certificate bridging creates secure connections between systems using different SSL Certificate types or configurations. This is especially important for enterprises running hybrid environments or connecting legacy systems with modern...
Understanding SSL Certificate Bridging
SSL Certificate bridging creates secure connections between systems using different SSL Certificate types or configurations. This is especially important for enterprises running hybrid environments or connecting legacy systems with modern...

Phishing Attacks and SSL Certificates
Phishing attacks typically involve fraudulent attempts to steal sensitive information by impersonating legitimate websites and businesses. Cybercriminals create convincing replicas of trusted sites to deceive users into sharing login credentials,...
Phishing Attacks and SSL Certificates
Phishing attacks typically involve fraudulent attempts to steal sensitive information by impersonating legitimate websites and businesses. Cybercriminals create convincing replicas of trusted sites to deceive users into sharing login credentials,...
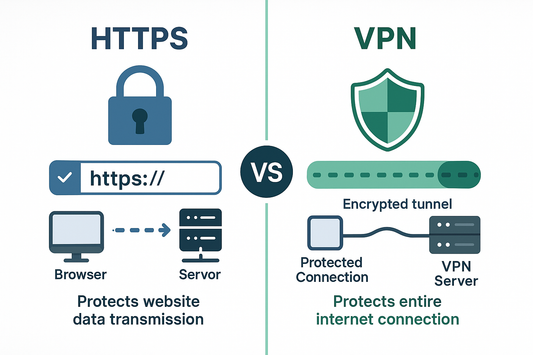
HTTPS vs VPN : Which Security Method Should You...
While both SSL Certificates and VPNs enhance online security, they serve different but complementary purposes. SSL Certificates secure specific website connections and verify site authenticity, while VPNs encrypt all internet...
HTTPS vs VPN : Which Security Method Should You...
While both SSL Certificates and VPNs enhance online security, they serve different but complementary purposes. SSL Certificates secure specific website connections and verify site authenticity, while VPNs encrypt all internet...
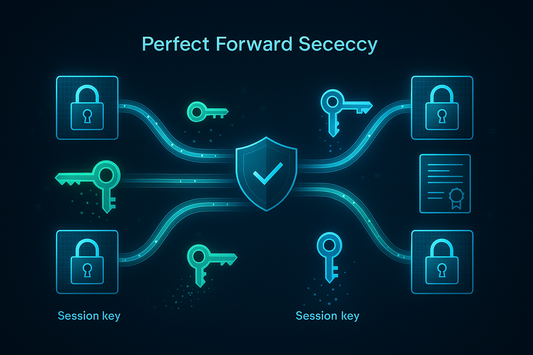
Perfect Forward Secrecy (PFS) : Enhanced SSL Se...
Perfect Forward Secrecy is an advanced encryption capability that generates unique session keys for each connection secured by a Trustico® SSL Certificate.
Perfect Forward Secrecy (PFS) : Enhanced SSL Se...
Perfect Forward Secrecy is an advanced encryption capability that generates unique session keys for each connection secured by a Trustico® SSL Certificate.

Understanding Shared SSL Certificates for Web S...
A shared SSL Certificate allows multiple websites or subdomains to use the same SSL Certificate for encrypting data transmissions. Trustico® SSL Certificates include both shared and dedicated options, giving businesses...
Understanding Shared SSL Certificates for Web S...
A shared SSL Certificate allows multiple websites or subdomains to use the same SSL Certificate for encrypting data transmissions. Trustico® SSL Certificates include both shared and dedicated options, giving businesses...

Understanding Domain Hijacking : Risks and Prot...
Domain hijacking occurs when malicious actors gain unauthorized control of domain names by compromising domain registrar accounts or exploiting vulnerabilities. This can lead to website defacement, e-mail interception, and loss...
Understanding Domain Hijacking : Risks and Prot...
Domain hijacking occurs when malicious actors gain unauthorized control of domain names by compromising domain registrar accounts or exploiting vulnerabilities. This can lead to website defacement, e-mail interception, and loss...
Stay Updated - Our RSS Feed
There's never a reason to miss a post! Subscribe to our Atom/RSS feed and get instant notifications when we publish new articles about SSL Certificates, security updates, and news. Use your favorite RSS reader or news aggregator.



